-
 chevron_right
chevron_right
Microsoft in damage-control mode, says it will prioritize security over AI
news.movim.eu / ArsTechnica · Thursday, 13 June - 20:38
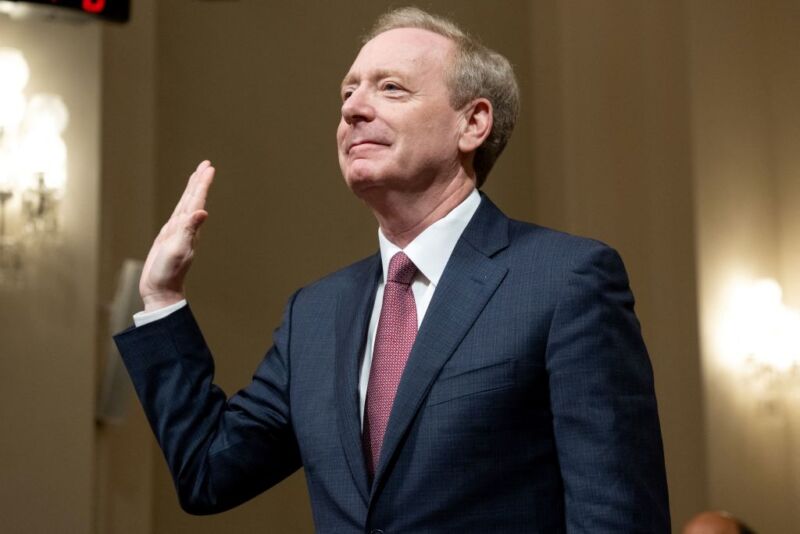
Enlarge / Brad Smith, vice chairman and president of Microsoft, is sworn in before testifying about Microsoft's cybersecurity work during a House Committee on Homeland Security hearing on Capitol Hill in Washington, DC, on June 13, 2024. (credit: SAUL LOEB / Contributor | AFP )
Microsoft is pivoting its company culture to make security a top priority, President Brad Smith testified to Congress on Thursday, promising that security will be "more important even than the company’s work on artificial intelligence."
Satya Nadella, Microsoft's CEO, "has taken on the responsibility personally to serve as the senior executive with overall accountability for Microsoft’s security," Smith told Congress.
His testimony comes after Microsoft admitted that it could have taken steps to prevent two aggressive nation-state cyberattacks from China and Russia .

